Compliance & Risk Suite
At NexaByte Innovation Private Limited, security, compliance and risk governance form the backbone of our payment infrastructure. We operate with globally aligned standards to deliver secure, encrypted and regulation-ready digital transactions.
Industry Certifications
Globally recognized security validations ensuring trust and protection.

PCI-DSS Certified
Secure processing and storage of cardholder data with strict encryption and monitoring controls.

ISO Aligned Security
Structured governance, risk management and operational control framework.

SAAR Compliance
Security Audit and Risk Assessment ensuring proactive risk mitigation.

VAPT Certified
Continuous vulnerability assessment and penetration testing protection.
Regulatory Compliance & Ecosystem Alignment
NexaByte operates within India’s regulated financial framework, ensuring secure digital transactions, strong governance controls and infrastructure aligned with national payment regulations.
RBI Compliance Framework
Aligned with Reserve Bank of India guidelines for payment systems and data security.
NPCI Infrastructure Standards
Secure transaction routing, digital authentication and operational reliability.
Secure Payment Channels
Protected processing of UPI, Card Payments, Net Banking with encrypted transaction layers.
Advanced Encryption Protocols
End-to-end encryption securing data in transit and at rest across distributed infrastructure.
Resilient Cloud Infrastructure
Controlled access, secure APIs, continuous monitoring and proactive risk mitigation controls.
Risk Management Framework
Our multi-layered security model ensures continuous protection, regulatory resilience and enterprise-grade infrastructure integrity.
NexaByte integrates predictive threat intelligence, real-time anomaly detection and regulatory aligned safeguards to protect every transaction across our digital payment ecosystem.
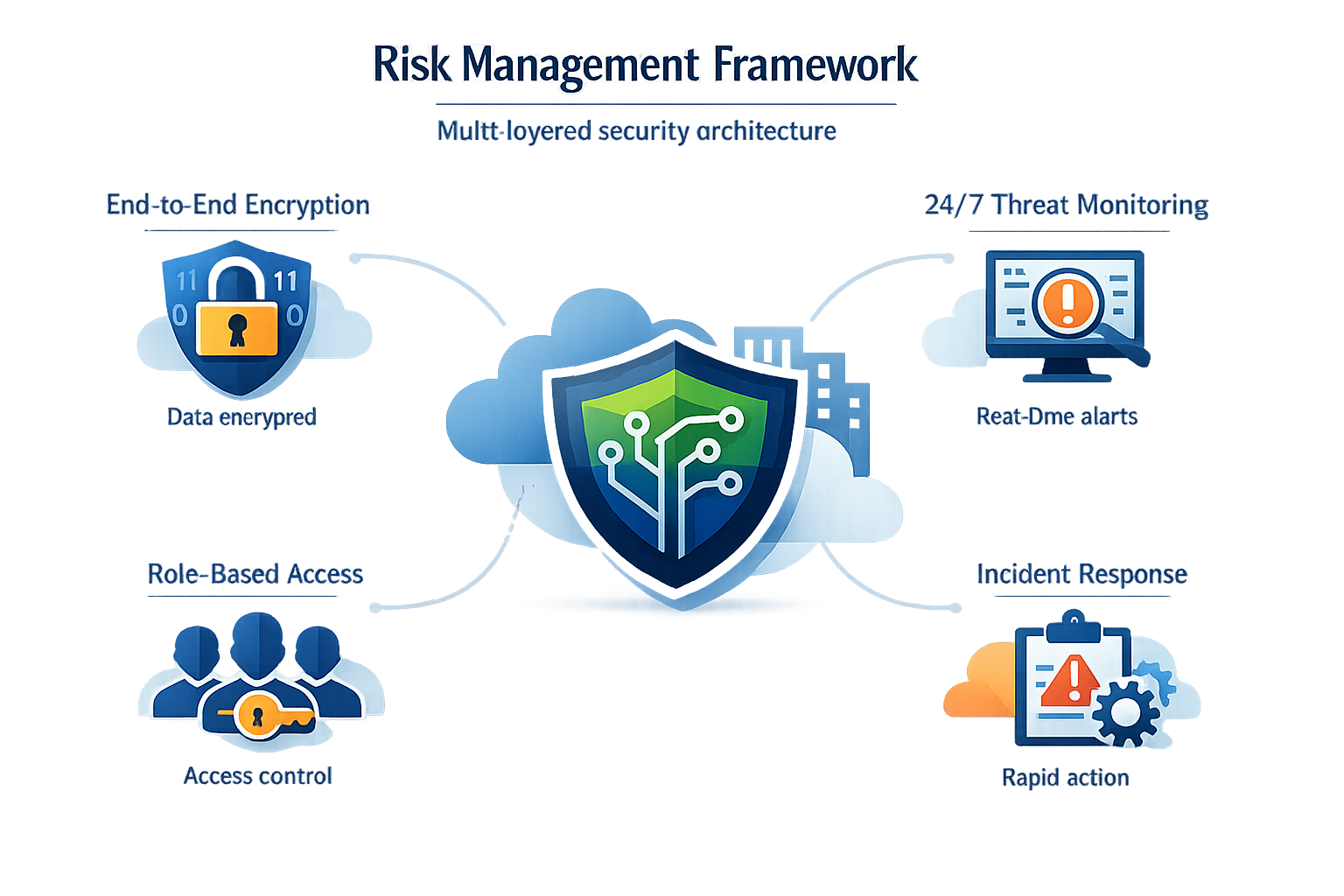
Encryption
Monitoring
Access Control
Incident Response
End-to-End Encryption Architecture
Every transaction processed through NexaByte is protected by enterprise-grade encryption protocols ensuring confidentiality, integrity and tamper-proof transmission across distributed systems.

24/7 Intelligent Threat Monitoring
AI-driven monitoring systems continuously analyze transactions to detect anomalies and prevent fraud in real time.
Real-Time Detection
Instant anomaly identification across transaction layers.
Behavioral Analysis
Pattern recognition to identify suspicious activities.
Automated Alerts
Immediate response triggers and risk mitigation workflow.
Role-Based Access Control
Our granular identity governance framework ensures that access to critical systems and payment infrastructure is strictly restricted to authorized users.
Multi-Layer Authentication
Advanced identity verification and layered login security.
Incident Response Framework
Structured mitigation strategy with real-time containment.

